INVOLUNTARY EMPLOYMENT SEPARATION / TERMINATION STRATEGIES
Version 3 Guide

ACKNOWLEDGEMENTS
This guide came out of my concern with the tragic 2019 shooting in Aurora Illinois and my conviction that we can do better The resulting documentation would not be possible without the help of the following individuals:
- Chris Olsen SAP
- John Friedlander, MS, CPP Guidepost Solutions, Inc.
- David Nicholas Washington, DC nonprofit
- Don Robinson, CTM Clinical Security Solutions LLC
- Mike Moorman, CPP, PCI, CSMP Yazaki North America, Inc.
- Tom Neer, Tom Neer – Behavioral Specialist. Office of Intelligence & Counterintelligence, U . S. Department of Energy, [email protected]
- Melissa Muir, JD Melissa Muir Consulting
- Jameson Ritter, CTM, CPP, PSP, PCI Threatwise Global LLC
- Gabrielle Thompson, PI, CPP Threat Assessment Consultant
- Ashlee Heavrin, Threat Manager The Kroger Co.
- John Rodriguez Empathic Security Cultures, LLC
Any organizational or business affiliation or endorsement is not intended and should not be inferred. Document is free to all but is not to be used for commercial purposes. © 2025
Sean A. Ahrens, CPP, CSC, FSyl, CHPA
Premise Liability Security Expert Witness Consultant
www.AhrensSecurity.com
Edits, ideas, thoughts for inclusion into this document? Please let me know:
[email protected]. Please include Involuntary Separation in subject.
Issue Date 04-15-21, Version 1
Issue Date 12-16-22, Version 2
Issue Date 10-28-25, Version 3
Amat Victoria Curam

Involuntary Employment Separation/Termination Strategies
INTRODUCTION
The following guidance for employment separations is made free for use and combines the thought leadership of multiple people from the Association of Threat Assessment Professionals (ATAP) This guide is an employer’s person-centric tool to manage and mitigate behavioral risk concerns before, during, and after the involuntary separation of an employee As such, a link to download this document in Word format is provided for customization to your respective environment.
Experience has shown that organizations are often unprepared to manage and respond to potential scenarios where employees proposed for separation
may act out, conduct sabotage or theft of proprietary (or classified) information, access personal data of fellow employees, and/or create backdoors to retain access subsequent to separation Each situation is unique and should be treated as such While there is not one prescriptive method to address behavioral risk at employment separation, certain preven- tative processes can help minimize the potential for harm to self or others This guide is intended as a starting point in assisting employers to proactively address separations This guide is a living document which will be reviewed and updated as additional best practices surface
TERMINATION
In the context of workplace threat management and supportive interventions, we intentionally avoid using terms such as “let go,” “terminated,” or “fired” when describing a separation These words carry inherently punitive, abrupt, and stigmatizing connotations that can undermine the broader
goals of a respectful, empathic, risk-informed, and human-centered approach The term “terminated” is used in this document due to its common use in human resources and legal contexts, though it conflicts with the supportive tone central to threat management
DEFINITIONS
Contained within this document are several definitions which may assist individuals and organizations who are developing processes and procedures related to involuntary separation/termination:
Behavioral Health: The scientific study of the emotions, behaviors and biology relating to a person’s mental wellbeing, their ability to function in everyday life, and their concept of self. “Behavioral Health” is the preferred term to “Mental Health.” Violence in the Federal Workplace, 2019.
Interview: A structured or semi-structured conversation with another person to gather information on the behavioral risk picture of a person of concern. The information solicited often centers around the who, what, where, why and how an act or event occurred.
Direct/Veiled Threat: Direct or implied communication or action that creates a reasonable fear that injury could occur or intentionally create emotional distress to another person. A direct threat is straightforward (“I’m going to kill you”) while a veiled threat is implied (“I could make my manager disappear if I wanted to”).
Employee Assistance Plan (EAP): An EAP plan refers to an Employee Assistance Program that is a confidential, employer-sponsored service designed to support employees with personal or work-related problems that may impact their job performance, health, or well-being
Pretext: A reason given in justification of a course of action that is not the real reason. For the purposes of this guide, a pretext might include a fabricated scenario to facilitate contact with a person of concern or to elicit information from the person of concern which will aid in the overall threat assessment.
Threats by Proxy: A threat directed by an aggressor to a person through a third party (i.e., hiring a programmer to write automatic threatening texts, a sister harasses her brother’s ex-wife.)
Behavioral Risk: Any particular behavior or behavior pattern which can strongly yet adversely affect health, safety, or adaptive functioning. Source: www.psychologydictionary.org.
- The Federal Bureau of Investigation’s report titled, “Making Prevention a Reality: Identifying, Assessing, and Managing the Threat of Targeted Attacks” (2017) is a valuable resource organizations can use to gain a better understanding of behavioral risk assessment and
- Be-on-the-lookout (BOLO): A BOLO is a notification issued by law enforcement or security personnel to alert others to watch for a specific person, vehicle, or situation that may pose a risk or require attention. A BOLO typically includes identifying details such as names, physical descriptions, photos, known associations, or behaviors of concern
Threat Management Team: A multi-disciplinary group of individuals from interdependent organizational departments (examples of departments that could be represented on the Team are Human Resources, Legal, Security, and Operations) that assemble to identify, evaluate, and address behavioral risk concerns, which may or may not include direct or implied threats, exhibited on/off company premises. Depending on situation, a threat management team may include ad hoc
members who are invited to participate on the team on an as needed basis.
DEFINITIONS (CONT.)
Workplace Violence: Unwanted, unsolicited behaviors, occurring within company-controlled property or locations associated with the company, that generate a reasonable concern for one’s safety, security or mental well-being. The behavior can be progressive, it can be immediate, or it can be accomplished through proxy.
- Examples of behaviors leading to reasonable safety concerns can include but are not limited to acts of physical violence, direct or indirect threats, verbal, nonverbal, and physical intimidation, implications or suggestions of violence, possession of weapons where prohibited, assault of any form, physical restraint or confinement, dangerous horseplay, loud, disruptive or angry language or behavior atypical of the work environment, commission of violent crime, or any act that a reasonable person would perceive as a threat of violence.
BACKGROUND
There are four areas of consideration within workplace violence. These include:

- Environmental factors (i.e., in high-crime area, work alone condition, handles cash or valuables, hot or stressful environments, proximity to houses of worship).
- Prevention approaches (i.e., training, policies, procedures target hardening through access control, badging, employee and visitor validation and vetting).
- Management approaches (i.e., threat assessment team, investigations, multidisciplinary threat management).
- Response measures (emergency response plans, training, exercises, coordination with law enforcement, crisis management, communications management). When evaluating law enforcement resources, it is important to establish a working relationship first with local law enforcement. Refer to Appendix B for additional guidance on how to build that relationship, prior to need.
This document is focused on preparedness but is intended to support any organization, regardless of whether they have an existing formal workplace violence program in place It also is intended as an informational resource for those who are concerned about an upcoming separation It’s a resource for those who have a concern about how an employee will respond to negative information and unfavorable developments.
Note: Effective workplace violence prevention should not solely rely on “feelings” about how an employee will respond to negative information and unfavorable developments Instead, gut feeling should be supported by the use of consistent and defensible processes and procedures to identify, assess, and mitigate potential threats
DISCLAIMER/NOTICE
This guide is for general informational and educational purposes only and is not legal advice Laws vary, so consult a qualified attorney for advice on your situation The intent of this document is to support Human Resources and other corporate administrative functions such as Behavioral Risk Management and Threat Management teams, and it should not be considered exhaustive If violence or harm seems imminent, or when in doubt, contact law enforcement (e g , 911), notify your organization’s threat management or behavioral threat assessment team, and seek assistance from external partners immediately.

STAFF CONTACT WITH EMPLOYEE
The decision to terminate/separate may arise out of an organizational process, which is typically marked by a Performance Improvement Plan (PIP) or progressive discipline process It may manifest from one or more policy violations Regardless of motivating factor(s) and whether a PIP has occurred, in most cases, there should be contact with the individual slated for separation prior to the separation in order to address and document the investigative or procedural process and gather critical information about the employee’s demeanor and their likely response to the separation
PRE-INVESTIGATIVE INTERVIEW CONSIDERATIONS
1. Separation will require an investigation or a performance improvement process. It is possible that corporate policy requires suspension/administrative leave during the investigation.
- Preparation is important. Apart from the performance issues or concerning behaviors exhibited by the employee, are there any known external stressors (e.g., financial, family, health) that have contributed to these issues and which may influence the employee’s response during the interview?
- It is important to consider how the employee may respond to an interview and the potential for the future investigation, suspension, and separation. Are there other stressors (e.g., financial, family, health, etc.) which may influence the employee’s response to an interview or their behaviors at the conclusion of the interview?
To the extent possible, the interview should be conducted in a manner that conveys empathy, ideally by someone with de-escalation training who is able to remain calm in the face of a potential emotional outburst. The interview should be conducted by someone with de-escalation training and the ability to remain calm in the face of potential emotional outburst. Potential questions and concerns of the employee should be anticipated so answers and directions can be provided by the interviewer in a direct, clear and concise manner.
2. Gathering the employee’s statement will be required in the majority of cases. Before the employee interview, consider whether suspension of that employee might occur at the conclusion of the meeting depending on the outcome of the investigation. Topics to consider:
☐ Will the suspension be with or without pay? Whenever possible, suspension with administrative pay is advisable.
☐ Plan to coordinate with Labor Relations, Human Resources, Corporate Security, and Legal, because even a suspension with pay may trigger the person to act out.
☐ The interview should be discreet and confidential and ideally conducted away from fellow employees. (i.e., manufacturing floor, break area/cafeteria).
☐ Interview the employee about their involvement in the concerning situation. Treat the employee with dignity and respect and avoid an interrogative atmosphere.
☐ Seek facts. Do not render opinions. Fully document the who, what, where, when, why, and how questions of the interview.
☐ Tie payments to the contingency of returning all company property, credentials, and keys, and stipulate that the employee not return to the workplace unannounced.
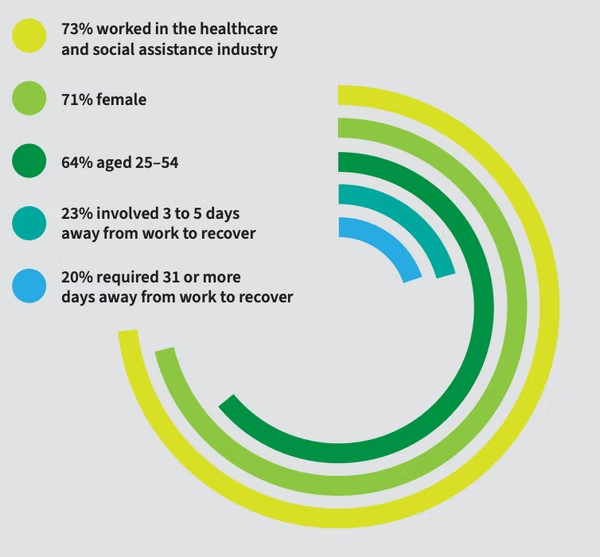
The Occupational Safety and Health Administration (OSHA) estimates more than 2 million individuals are affected by workplace violence every year.
According to the Bureau of Labor Statistics (2018) 20,790 workers in private industry experienced trauma from nonfatal workplace violence in 2018.
These incidents required days away from work. Of those victims who experienced trauma from workplace violence:


PREPARING FOR AN INVOLUNTARY SEPARATION
When working with someone who has the potential to act out, the core goal in the process should be to do so deliberately, which ensures a safe workplace, protects other employees, and mitigates long-term threats One important way to pursue the overall aim is to treat an employee who will be or is being separated with dignity and respect As a general guideline, consider the situation from your own perspective For instance, meeting with a staff member in front of their peers and calling them back to your office, may not be the best approach In short, treat people in the same manner as you want to be treated
ACCORDING TO THE VIOLENCE PROJECT
70%
OF SHOOTINGS ARE BECAUSE OF SOME TYPE OF EMPLOYMENT ISSUE
1. The first question is: Why is this person’s employment ending?
Is the termination performance-related? If so, were they on a PIP?
☐ Is the termination because of a Reduction In Force (RIF) or workforce downsizing?
–RIFs occur periodically in the U.S. Government and military, and also within private industry. In such cases, especially in recent months as DOGE has RIF’d federal workers attached to intelligence agencies, the potential risk is not so much about WPV, as it is being so disgruntled as to steal and sell trade secrets to the highest bidder (i.e., China).
☐ Has a separation event or policy infraction occurred previously with this individual?
☐ Does the employee possess unique knowledge/information which would allow the employee to access the location, information, or processes which could be used by the employee to retaliate against the company after the separation or termination or prepare for such action before separation or termination is finalized?
☐ How close is the employee to retirement and how will the separation impact the employee and their family financially?

Has a proper, neutral investigation been conducted? Ideally, management will address the following questions at least one week prior to the interview or investigation However, there might be some urgent situations where decisions will need to be made more quickly “Yes” answers could indicate greater concern and the need for additional planning or support, such as engagement with a Threat Management Team
☐ Has the employee reacted to disciplinary information negatively in the past?
- Has the employee previously made threats to bosses, peers, or subordinates?
- Has the employee shown a propensity to blame others for their actions?
- Has the employee indicated they are being victimized by their bosses or the company?
- Does the employee feel they have multiple injustices or unfair action against them?
- In what ways did the employee negatively react and to what degree? Have they yelled? Were they visually holding back their outburst? Did you observe body language/signs such as clenched teeth, balled up fists, flushed face, or intense staring?
☐ Has the employee ever presented behavioral risk concerns?
☐ Has the employee shown other concerning behavioral changes?
☐ Do you know if the employee has any recent or current personal stressors that are adding to the disciplinary process?
- How will the disciplinary process and potential separation impact existing personal stressors?
☐ Is the employee without personal support (family/friends)?
☐ To your knowledge, are there concerns about the employee regarding theft or incidents of sabotage via their access to sensitive or potentially dangerous organizational materials?
☐ Do you know if the person has access to weapons? Does their employment require the use of weapons, tools or implements (i.e., armed security/law enforcement personnel, custodian, food preparation)?
–Consider how will the disciplinary process and potential separation impact existing personal stressors? Does the employee have a work visa?

IMMEDIATE POLICY VIOLATIONS
If an obvious policy violation has occurred, which is directly witnessed or corroborated quickly through an investigation, consider immediate suspension with administrative pay. Questions to consider:
☐ Is it possible to take an approach of progressive discipline?
☐ If suspension is possible, prepare a packet of information outlining the process, steps, timeline, and pre-defined touch points when the employee will be contacted to update them on their employment status.
☐ Consider offering or requiring Employee Assistance Program (EAP) and/or evaluation for Family and Medical Leave Act (FMLA) or Short-Term Disability (STD) if behavioral health appears to be a concern.
☐ Suspensions should not be a personal decision but reflected in policy. The investigator is only following corporate policy rather than appearing biased. Ensure you have a policy that addresses this.
☐ Provide a single, clearly defined point of contact for the employee to contact to address outstanding items, questions and concerns following separation.

INVOLUNTARY SEPARATION CHECKLIST
It is critical to ask introspective or direct questions about the person whose employment is ending. “Yes” answers may indicate a greater concern and the need for additional planning or support, such as engagement with a Threat Management Team.
☐ Is the employee still in the workplace?
☐ Have they been sent home without pay?
☐ Is the person aware separation may be imminent? Have they been part of a PIP?
☐ Have coworkers expressed concerns about how the person may react if/when job separation occurs?
☐ Do employees/colleagues describe the employee as combative, hot-headed, fragile, or toxic? Do employees/colleagues express being in fear that the employee might act out violently, whether supported by examples or not?
☐ Is the person without a support group? Partner or significant other? Family? Are these individuals not local?
☐ Does the employee have an unsupportive family life?
☐ Has the employee worked with the employer for a significant amount of time?
☐ Does the person have close friends at work? Supportive coworkers?
☐ Is the employee local to the facility? Do they reside nearby?
☐ Does the individual dislike the person conducting the separation?
☐ Is the person who complained scheduled to take part in the meeting? [The complainant should not participate in the separation meeting.]
☐ Does the employee have a violent criminal history? Has a verified/accurate criminal history been obtained for the individual?
☐ Does the employee have a history of using violence to resolve conflict?
☐ Are there no “soft landing” options available? (For example: vested benefits, severance pay, effective date for coverage or leave options (severance pay, extended leave benefits, [effective date for coverage or leave options]), employment outplacement, employment assistance, or benefit extensions including access to EAP services and health insurance.)
☐ Is a criminal history not being considered?
☐ What is the individual sharing publicly on social media? Are they venting frustration or expressing anger toward the organization or its employees, or posting direct or veiled threats (i.e., “leakage”)?
☐ Has a formal threat assessment been conducted, and, if so, is it being considered or dismissed?
☐ Is there agreement among the management team that separation is the best option?
☐ Have you not considered the opinion(s) of the threat manager?
☐ Are there potential risks beyond WPV, i.e. theft of proprietary information or personal employee information, or sabotage of computer systems?
☐ Is there no plan/emergency protocol in the event of escalation (potentially anonymizing targeted individuals contact information)?
☐ Have state labor laws not been consulted regarding prerequisites to the separation?

SEPARATION PLANNING & MEETING
“Amat Victoria Curam” (Victory Loves Preparation) emphasizes the primary focus, which is to plan, plan again, and continue to plan when dealing with an employee exhibiting behaviors of concern.
1. Absent imminent threats, you should never be rushed to make a separation. If planning, legal, security or other needs are still pending, consider extending a paid leave “pending investigation” period to extend as long as it takes to complete investigation and implement all appropriate safe plans before the separation conversation.
2. Prior to any high-risk separation, engage the organization’s established TMT or a designated TMT representative to assess potential risks and mitigation strategies.
- If a formal TMT program is not in place, consult with an internal Safety and Security representative or an external subject matter expert (SME) with experience in behavioral threat management.
- TMT consultation should inform planning, including participant selection, location considerations, security measures, and post-separation monitoring.
- Ensure that threat mitigation strategies align with organizational policies, legal considerations, and best practices for workplace safety.
3. What factors could aggravate, or conversely, help mitigate potential risks. Who is in the best position to observe or monitor the employee post-separation?
4. Has management decided who is the best person to do this interview?
5. Prepare a brief script, consider what-if scenarios, and how the individual leading the meeting would react to various situations. In certain corporations, the manager leading the termination meeting might need to be trained prior to conducting the meeting. Recognize and involve others (Legal, Labor, Union Representatives, Security) in all aspects of the separation process. Where applicable, consider involvement by law enforcement as outside support. The script should be brief but maintain the respect and dignity of the person. Organization representatives should not be baited into an argument, and the focus is being direct, firm, and supportive.
Where possible and safe, structure the separation conversations in two parts: In the first part of the conversation, give the person 3–4 key pieces of information (your employment is ending now, your pay will continue until (insert date), we won’t contest unemployment, confirm contact information and set a meeting for next day, review key points for second conversation). For the second part of the conversation:

– Ask if the employee has questions.
– Answer any open questions from the first meeting with the employee.
– Describe the timeline to the employee (last paycheck, insurance end date and EAP end date).
– Provide additional details that weren’t covered in first meeting (whether a reference will be provided, arrangements for any personal effects).

6. Given the organizational delegations/assignments and dynamics, consider the best person from the organization to deliver the separation notice.
– Will the separation be done by an individual (i.e., manager, human resources staff) who is properly trained in the separation of a person who may act out?
– Identify participants. As few as possible, but not less than two individuals.
– Considerations should be given to how the subject employee will respond to the participants and number of participants. Other participants can include:
- Union steward.
- Only those with a need to know should be aware of the separation meeting.
– Presence of witnesses.
- Only people that absolutely have to be present should be. The primary facilitator should be on their own camera. Exclusive use of conference room only video should be discouraged.
- Have a witness (HR representative or manager) present during the meeting to ensure an unbiased account of the interaction.
- If there are other company personnel, i.e., from the employer’s staff, who are in the room or joining online, identify who they are and why they are present.
- Identify who is in the room/transparency and protection for their privacy.
- Always be transparent about who’s in the room.
- Announce any person who arrives late to the meeting and their reason for being present. Ideally identify these persons who will join the call.
- If the employee has others attending in support or a counseling role, e.g., a union representative, the employee should identify them as well and their function. If the employee has retained legal counsel and the person has joined the meeting without prior coordination with human resources, etc., it will need to be decided whether to continue the meeting or reschedule when the company’s legal counsel can attend.
- Undesirable participants
– No students/interns or junior staff members.
– No staff/employees involved in complaint that led to a separation decision.
– No immediate supervisor or manager if the subject employee has a history of hostility, conflict, or an unresolved grievance with them, unrelated to the separation decision. When applicable, an alternative representative should be selected to avoid unnecessary tension or escalation. - Desirable participant
– Someone whom the employee respects or admires (which might encourage the employee to act appropriately).

7. Thoughtfully consider the location.
– Off-site, on-site or remote (phone, virtual meeting)
- Consider off-site.
- The method of conducting the separation meeting should be carefully considered. Remote separations are generally discouraged; however, they should be prioritized when a separation is identified as high-risk, particularly in cases where safety concerns exist. Additionally, as remote interactions have become more common post-COVID and some employees may be more comfortable with virtual discussions, a respectful and structured remote separation may be the most appropriate approach in certain situations. Refer to Appendix B for additional resources on remote separations. On-site physical locations where separation shall occur should have multiple exits.
– Near an exterior wall that is near an exit.
– Arrange seating in the room so that the employee does not feel boxed in. Seating should also allow the employer direct access to an exit door.
– Choose a room where doors swing outward from the room.
– Consider the employee’s parking and building access when selecting a location. Also factor in how the employee will depart the facility if they have a car on premises and what will allow for a smooth and safe departure.

- Have an area outside the room where the employee can securely leave personal belongings such as coats, lunch containers, backpacks, gym bags, etc. Do not let the employee bring any of these items into the room with them. Take off jackets/sweatshirts, etc., if appropriate.
- Away from employee congregation, gathering spots, or administration areas.
- Away from peer group – maintain dignity and coordinate a discreet means of exit.
- Contact security/law enforcement to be present and have additional staff to monitor area. Note: Detectable security includes a law enforcement observable presence could cause an adverse visible reaction.
– Thoughtfully consider day and time, if possible
- The designated day for separation is based on work schedule/hours. While most agree separation on a Friday is not ideal, there may be extenuating circumstances, or the employee may work on schedule that is outside of a normal work week. The intent is to give the opportunity for the staff member to contact co-workers or other staff members, to ask questions which will assist with the trauma of the separation and avoid a time where the employee “broods” over the event without opportunity to vent. The best separation date will be driven by workdays and times, and should not be considered absolute for all workspaces/departments and staff. Environmental factors such as the need for safe distancing and workspace considerations may also influence scheduling.
– Personal belongings
- Prepare a plan for personal belongings.
– Will the separated employee be allowed to gather their personal belongings? As a default, separated employees should not be allowed to personally retrieve their belongings, to minimize risks. Instead, a designated individual should gather and securely return the items. If an exception is made, establish a scheduled time and supervised process that prioritizes safety and preserves the employee’s dignity.
– Employees should only be allowed into the building after hours, in a supervised capacity.

– Two staff members should escort employee. Do not allow employee to pick up at the facility unattended; do not let employees go to other locations than their workspace.
- Generally speaking, from a safety perspective, it is best not to allow employees to gather their belongings themselves. This step might also lessen the likelihood of embarrassment and protect their dignity. One downside is that the employee could claim that their belongings were damaged, some are missing, etc. Decisions on this topic should be made in the context of overall safety.
– Thoughtfully consider how to retrieve organization-owned items (i.e., ID card, access cards, computer, phone, equipment, etc.) before last payment or compensation.
– Do not make the employee return to provide work equipment. Arrange for courier service to obtain all work equipment not on their possession at the separation meeting.
- Have options for retrieving personal belongings.
– Packing/shipping list of itemized contents being returned to employee.
- If an employee has belongings at the facility in a locker or office, then request permission to access items. As allowed by policy, cut locks. If there is damage to personal property, provide restitution for any damage to which should exceed expected value.
- Segregate organizationally owned items from personal belongings.
- Inventory and professionally pack items for return to employee.
- Have two managers involved in documenting, inventorying, and photographing all employee belongings, and signing inventory sheets.
- Arrange for secure delivery (i.e., FedEx, courier, etc.) to employee’s residence. Notify the employee when it will be delivered and require signature. Confirm and memorialize the tracking receipt.
8. Additional controls
– Ensure the employee is provided with a single point of contact (POC) within the company for any follow-up questions or concerns. This designated individual should be clearly identified in the communication packet to provide consistency and a cohesive message throughout the transition process.
– Evaluate controls to be used. These include, but are not limited to:
- Introduce EAP and provide direct contact information to assigned case manager.
- Job/hire employment services.
- References. What will organization say if contacted by potential future employers? [Be clear to avoid future confusion or anger.]
- Extension of health insurance.
- Pay.
– Paid leave?
– Pay extension?
– Stipends/scheduled payments?
– Severance packages?
– As allowable, donation of company equipment? (i.e., let them keep their phone/computer, etc. after wiping)
- For high-risk separations, do not contest unemployment claims. To do so may further antagonize the individual against the organization and its leaders or employees. Highlight to employee all that the company is doing to help the employee on the way out and to enable the employee to transition or to return to future success.

- Prepare a communication packet containing information and resource phone numbers. Ideally, have a last check at the meeting. If this is not possible, identify when they will receive their check, and make sure it arrives. Consider courier, or overnight guaranteed service if not by direct deposit.
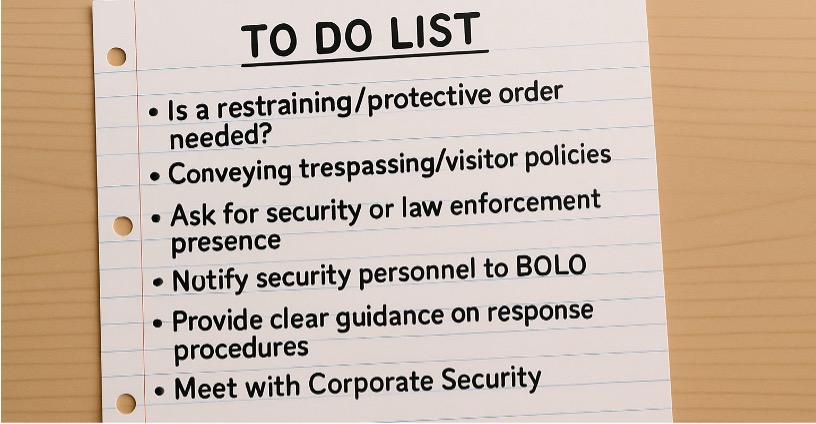
- Conveying trespassing/visitor policies prior to the separation discussion conclusion.
- Further considerations
– Is a restraining/protective order needed? This should be done in consultation with a behavioral/mental health professional, corporate security, and a threat management team.
– Conveying trespassing/visitor policies. This requires these policies are in place and communicated to employees.
– Ask for security or law enforcement presence, special patrols after employee departure, or ask police if they can stage a police vehicle at employee entrance. Position police vehicles for optimum visibility.
– After separation and while preserving the dignity of the separated employee, notify all appropriate security personnel, including contract personnel to Be-On-the-Lookout (BOLO) for the employee attempting to gain access.
– Place a photo into the separation file and ensure that it is communicated into a security pass-down book.
– Ensure the BOLO includes at least the employee’s name, aliases, identification information, photograph and vehicle information.
– Provide clear guidance on what response procedures are desired for anyone encountering employee post separation.
- A person’s separation should not be broadly disclosed; however, front-line leadership and other relevant personnel should be notified on a need-to-know basis. This ensures they are aware of the individual’s change in employment status and can respond appropriately if the former employee attempts to access the workplace. Additionally, organizations can reinforce general personal safety and building access procedures without directly referencing the separation.
– Meet with Corporate Security to discuss target hardening concepts and to develop a collaborative security plan.
– Victims
- If the employee threatened another employee or employees during the termination meeting, notify the potential victims.
- Determine whether targeted victim employees and coworkers feel safe and consider enhanced facility security such as:
– Additional security staffing
– Relocation
– Assigned parking space close to building entrance and within high visibility
– Rental car
- Home security
- Vehicle security
- Online anonymizing services (Note: online anonymizing services can take up to one year to eliminate publicly available data.)
– Additional thoughts
- How will you share information about the employee’s separation with coworkers? (Established talking points.) Ensure information shared is truthful, comfortable for the provider to share, respectful of the separating employee, and maintain the dignity of all involved.
- If questioned by other employees on why the separation occurred, it is best to advise that the reason for employees’ separations is confidential, unless a predetermined statement has been requested by the employee and Legal has approved it.
- Ask the employee how their separation should be communicated to other staff. As allowable, communicate these messages to staff. Ask if they would like to have a personal message emailed on their behalf to staff.
- Do not refute an employee’s perspective on how the separation occurred with other employees. If questioned by other employees, why the separation occurred, simply respond “I don’t know, I wasn’t involved” or “the person resigned” are appropriate answers. Avoid creating conflict with the employee and their former coworkers.
- Legal Elements:
– Other factors may impact the separation. Be sure to check with HR for any pertinent state labor laws that may dictate a requirements/schedule for a separation. For example, California requires an accurate final paycheck be delivered upon termination. Any decision regarding the timing of a termination/separation must be coordinated with all stakeholders.
- Emergency Protocols:
– Ensure that there is a clear and accessible emergency protocol in case the situation escalates during the separation.
– Process for notifying individuals who might be threatened by the employee to contacting law enforcement when appropriate.
- Incident Response Plan
– In some instances, separated employees might have a right to return to the workplace, i.e. healthcare or retail (if the employee will be told they are still allowed to shop at the store, etc.) Update policies, procedures regarding trespassing and returning to the former work location, unless it’s legally permitted.
– Develop a detailed incident response plan outlining actions to be taken during the separation.
– Review and rehearse the plan with the team to ensure everyone understands their responsibilities.
– Ensure that the remote setup (current work-from-home environment) is secure and minimizes the ability of the employee to access sensitive information. Ensure you can shut down their access to their computer once the meeting ends.
– As appropriate, provide employee photograph and vehicle information (if known) to law enforcement/security personnel with a “do not permit re-entry warning” to be maintained at security/reception areas.

SEPARATION DAY
The key to involuntary separation is rooted in respect and the willingness to support the employee and maintain the employee’s dignity with the opportunity for an honorable exit.
1. Separation day
- The employee should have no prior knowledge of the decision or any planning involved. The separation should appear unanticipated from the employee’s perspective, reducing the risk of counter planning.
- Scan employee’s social media posts to ascertain if “leakage” is present.
– If so, postpone separation meeting, continue to pay, and seek outside help.
- Pre-screen the designated meeting area and review seating, look for and remove any potential improvised weapons.
- Confirm attendance by meeting participants, police, security, etc. Separation should be conducted with a minimum participation of two designated individuals.
2. On-site Meeting
- Ideally brief, scripted according to employee’s specific circumstance and personality, and rehearsed for familiarity with statements to be conveyed.
- The separation meeting should be brief, ideally no longer than 15 minutes. Tissue, food (candy bars), and water should be on-hand for emotional response.
- Refer to the specific policy violation or organizational policy that led to the separation, rather than framing the decision around behavior or personal narratives. Maintain a factual, policy-based approach to ensure clarity and consistency.
- Have all separation documents prepared prior to the actual separation process.
- Acknowledge that documents may be overwhelming and difficult to process in these circumstances. Offer a resource to answer questions and set follow-up conversation to review documents, especially paperwork related to insurance and unemployment.
- Refer to the reason for the separation, do not engage in attempts to make conditions personal.
- During separation
– Revoke/suspend/disable computer and access control privileges.
– Evaluate other systems that may be at risk and take appropriate actions to protect those assets.
- Threats during meeting: Reassess for potential need for restraining or protective order.
• If an employee makes threats during the meeting, safely conclude the meeting, send the employee home, and notify any employees who might have been threatened. Verify they depart the premises. Is a security escort needed?
• If appropriate, request security or law enforcement presence after employee departure. An additional consideration to be discussed and considered in consultation with corporate security and a threat management team is the use of a marked police or security unit at highly visible locations such as the employee entrance or parking lot. Sometimes this can be productive and warranted, and in other instances it may be counterproductive.
3. Body language/verbal language
- Maintain eye contact, but avoid staring.
- The employer representative should avoid unnecessary movement and be conscious of facial expressions, or laughter, smirks, grinding teeth, flushed face, clenched hands or similar. If observed, note these non-verbal cues, ask if they are okay and whether they would like to continue.
- Be vigilant about the employee’s emotional response. If the situation becomes tense or threatening, have a plan in place to stop the meeting quickly.
- Monitor for body language by the employee: clenched teeth, balled up fists, flushed face, intense staring. If observed, communicate that you have recognized these behaviors and ask if they are okay. Offer food, water, tissues, etc.
4. Conclude separation meeting, deliver separation paperwork, and separation packet.
- Collect parking pass, keys, tools, materials, computers, access control cards. If applicable, return to HR.
– Identify consequences for unreturned items (i.e., laptops, phones, etc.).
- Have EAP information available to discuss with, and offer to, employee.
– If possible, extend EAP benefits beyond the separation date.
– Mention EAP program features (financial or legal counseling, EAP services available to family members).
- Identify milestone dates, follow-up actions, and touchpoints with the separated employee.
– Employment packages/milestones/calendar dates create opportunities for touchpoints with the separated employee.
- Schedule time to recover personal items.
- Determine who will escort the employee and if security or law enforcement are required. Have two staff members escort the employee out of the facility discretely to their car or arranged transportation.
- Immediately communicate to security, managers, and staff the outcome of the proceedings. To the extent possible, the separation should be characterized as a “parting of ways,” along with wishing the person success.

POST-SEPARATION MONITORING
One underutilized tactic in a separation process is post-separation monitoring. Human Resources personnel can use follow-up communication and ongoing support to gauge the demeanor of the separated employee. Monitoring can involve managers, corporate security, human resources, or even former peers. The intent is to find out if there are any vocal or body language cues which may suggest animosity towards the employer or its employees. The following is suggested as a monitoring approach:
1. After the announcement, honor your commitments fully.
2. Where possible, inventory and monitor social media, and maintain search alerts for the employee and the company over a determined course of time.
3. Consider identifying someone who can serve as a third-party intermediary or “pulse checker” for the separated employee after the separation meeting concludes. Is there someone with whom the employee is close to who can informally help monitor the employee’s reaction to separation for the escalation of new threats?
4. Continue monitoring relevant social media profiles in a manner undetectable to the employee to gauge coping and presence of “leakage” — direct or veiled threats or videos.
5. All follow-up contact should be conducted remotely whenever possible to prioritize safety. Any necessary documents or materials should be delivered via email or shipped to the former employee, eliminating the need for in-person meetings.
- If in person, one option is to suggest meeting at a public location such as a coffee shop or hotel lobby. Note that this could expose patrons and members of the public to violence and increases the company’s liability. If utilizing this option, consider having undetectable security present in the event the employee acts inappropriately.
- 1 day follow-up by Human Resources.
– Offer meaningful support.
– The conversation should cover unemployment, dates of final pay, vacation payout, health insurance benefits and options, other personal items, and questions the person may have.
– If in-person, propose meeting in a public place (coffee shop, for example) of the person’s choice near their residence.
– Document the call and demeanor.
- 1 week follow-up by former peers.
– As allowable, find out any concerns from coworkers or persons who are close to the individual.
– Document peer responses and their observations.
- 4 weeks follow-up by Human Resources (verify final pay, upcoming end to insurance or other benefits, or other dates related to employment).
– Offer additional controls.
• Ask how they’re doing.
• Offer additional job placement support.
• Document call and demeanor.
- 4 weeks and beyond.
– Touch base with peers and see if they have spoken to the employee. Ask how the previously separated person is doing. Have they gotten a new job? Document file with findings.
– Continue to periodically monitor public social networking profiles.
- For significant concerns, a Private Investigator could monitor/surveil the individual over a period of time to ascertain planning or reconnaissance that may be occurring.
– Consult the Corporate Security legal department prior to hiring.
– Obtain investigation briefs from the investigator.
– Ensure the Private Investigator is aware of the importance of not being detected, even if they lose the employee. In such cases, the Private Investigator should be instructed to contact you (immediately or within a predetermined time frame based on the location of the employee vs. victim/protected site).

closing considerations
Controls identified are often supported by policies and procedures. Ideally, the following policies, charters and, where applicable, procedures should be in place prior to an involuntary separation process. These include:
- Proactively developing telepresence protocols is essential for ensuring safe and consistent remote interactions. This is particularly important for separation discussions. It ensures that these conversations are handled with the same care, structure, and security as in-person meetings. (Refer to Appendix B for additional strategies and recommended methods.)
- Creation of a Workplace Violence Prevention (WPV) program team with leadership support and commitment.
- Establishment of preventative strategies:
– Develop a Threat Assessment Team (TAT) and processes for activating that team.
– Create assessment tools to evaluate and assess the probability that a person may act out.
– Scope to include all persons and all locations where business will occur, including any threats by proxy.
– Work with corporate security, legal, and the threat management team to assess the ability to secure psychological support for certain situations.
POLICY AND EMPLOYEE MANUAL AND OTHER IDEAS
- Workplace Violence Policy, including organizational action and consequences for unacceptable behavior from employees.
- Threat Management Team (TMT) creation, implementation, and development.
– Exercise team through tabletop exercises and ongoing training.
- Weapons Policy.
- Workplace Violence Prevention and Intervention Program
– Exercise team in mock involuntary separation processes.
- Denial of Access and/or Trespassing Policy.
- Requirements for Protective Order/Restraining Order Communication.
- BOLO (Be-On-the-Lookout) Notification Process.
- Emergency Contacts:

– Legal
– Corporate Security
– Insurance and Benefit Contacts
– EAP Intake Contacts
– Crisis Management Team
• Other Counseling
• Behavioral Psychologist
- Create and leverage a reporting system for concerning behavior and suspicious activity to identify and assess potential threats.
- Train employees on how to recognize and report concerning or suspicious activity.
- Train managers on how to assess and triage reports of concerning behavior and suspicious activity.
- Maximize cross-departmental collaboration for assessing and managing concerning behavior or suspicious activity.
- Establish proactive relationships with law enforcement before incidents occur — this is essential for effective threat management.
– Build trust, streamline communication, and ensure internal teams and external responders are aligned for safety.
– Early collaboration supports informed decision-making, coordinated response planning, and faster access to support.
– Refer to Appendix D for guidance on building these partnerships.
- Debriefing:
– After separation, immediately debrief with the team to discuss events and any immediate concerns.
– Review the separation process to identify strengths and areas for improvement.
– Document expressions, body language, and other indicators that could inform threat assessment and mitigation.
- Close-Out Communication:
– Identify and document all statements, expressions, and body language.
– These observations should be reviewed by the Threat Assessment Team for ongoing evaluation and the development of mitigation plans.

- Record Keeping:
– Keep detailed records of all communications and actions taken during the separation process as part of the employee’s file.
– If the meeting was recorded, share the recording with the separated employee, while noting potential concerns about posting it on social media.
– Obtain a recent high-resolution photo of the person being separated for the file.
– Ensure that documentation addresses the who, what, when, where, and why of the separation process, with all actions and communications properly dated and time-stamped.
APPENDIX A
INVOLUNTARY SEPARATION CHECKLIST
SECTION 1: Complete the following safety questions for all separations If a felony is present or you get a ‘YES’ response for two or more items, contact human resources (HR), management or threat assessment team
| Screening Questions (Who/What/When/Why) | Notes |
|---|---|
| Employee position | |
| Department | |
| Manager | |
| Duration of employment | |
| Reason for separation | |
| Was a criminal background check completed at time of hire? | If any felonies reported, describe: |
| Timeline for separation | |
| Is employee still on campus or on administrative leave? | If on administrative leave, with or without pay? |
| Is the case being investigated by Employee Relations, HR, Title 9? | Has the employee been interviewed? If HR is investigating, who is the investigator? |
| Is the employee aware of separation? | If yes, possible, or imminent? |
| Does the employee show animosity or hostility toward anyone involved with the investigation or the separation meeting? | Do any of these people need to be present during the separation meeting? |
| Does the employee have any support? | Spouse, family, therapist? Are they local? |
| Any known behavioral health concerns or stressors and/or substance abuse? | |
| Any known history of workplace violence, interest in workplace violence/mass attacks, or interest/access to weapons? | |
| Has the employee reacted threateningly, violently or otherwise inappropriately? | |
| ADDITIONAL PERTINENT INFORMATION: |
This checklist should be completed as far in advance of a pending separation as possible
SECTION 2: HR completes the following safety questions for all separations If you get a ‘YES’ response for 2 or more, contact the threat assessor or corporate security management
| Safety Questions | Notes |
|---|---|
| Has the employee reacted violently to coaching from manager and/or HR? | |
| To your knowledge, are there concerns about the employee regarding potential of sabotage or theft, or access to sensitive or potentially dangerous materials? | |
| Has the employee shown behavioral changes or conditions that may be of concern? | |
| Is the person under stress related to this action (medical, family, divorce, etc.)? | |
| Have there been warning signs, which would cause a negative reaction (fascination with weapons, leakage, suicidal/homicidal ideation, or news related events)? | |
| Have there been any warning signs which would indicate a negative reaction (fascination with weapons and workplace violence/mass attacks)? | |
| Are you aware of coworkers of the employee expressing concerns about how the employee has acted previously or how the employee might react to negative circumstances? | |
| Does the person have access to weapons? Has the person expressed a desire to obtain weapons? |
SECTION 3: Conduct pre-separation meeting with team Review facts of the case, including corrective action processes and employee responses
| Plan the Separation Meeting | Notes |
|---|---|
| Employee Schedule | |
| Date and Time of Meeting (based on end-of-week work schedule for employee) | |
| Location (Remotely/telepresence if possible), Refer to Appendix B for additional resources on telepresence separation. | |
| Other factors that could affect or elevate the risk of separation on that day? | |
| Separation meeting attendees (Who will represent the organization)? Only those absolutely necessary should attend a separation meeting. | |
| Do we need a PD or security standby? Have Law Enforcement contacts been established? | |
| Personal belongings: Who’s going to box up? How will they be delivered? Consult with legal before boxing up someone’s personal belongings. | |
| How and when will you collect company-issued equipment? Will you let them keep the equipment? | |
| Notify organization access controls and/or any other applicable offices/departments/banks/etc. to remove access. | |
| Communicate who will be the main point of contact to the employee. | |
| Discuss safety plan for team conducting the separation meeting. | |
| Prepare the separation package (next steps info; benefits, final paycheck, Job Service, EAP, etc.)/severance package. | |
| A small investment in extra benefits is an investment in safety. | |
| HR will notify manager. | |
| HR will notify union. | |
| Who will notify employee (Manager, Union, Other)? |
SECTION 4:
| Separation Meeting | Notes |
|---|---|
| Policy infraction and/or read separation letter. | |
| Deliver separation paperwork and separation packet. | |
| Communicate trespass notice if applicable. | |
| Collect keys, tools, materials, computers, access control cards (if applicable, return to HR). | |
| If necessary, have law enforcement present while the individual recovers personal items OR consult with legal to pack personal belongings and ship them. | |
| Escort employee out of the facility. | |
| Communicate to security and management staff; how will you share information about the employee’s separation with coworkers? | |
| Have you sought legal input? | |
| Have you documented the meeting and maintained records? |
SECTION 5: Monitor for any concerns that arise: unwanted phone calls, appearances, emails, etc involving anyone related to the workplace Monitor for threats of lawsuits and social media leakage Report to Safety Team if any of the previous items are brought to your attention
APPENDIX B
REMOTE SEPARATION
Understanding telepresence separations
This section relates to one-on-one engagements and does not address mass layoffs or reductions in force (RIF) and further addresses remoted presences (video and audio) While telephone could be used, the preferred method in addressing a remote separation would be via telepresence with video The separation process can be profoundly challenging for those whose employment is ending, and also for those making the decision Senior leaders and managers might not always have the benefit of HR personnel involvement in the termination meeting A traditional downsizing procedure can now become fractured through remote separation and can create serious concerns Despite ongoing Return to Office (RTO) efforts, many positions remain remote or hybrid Consideration should be given to an employee’s work status (on-site, hybrid, on leave) when deciding if a remote termination separation is appropriate In short, while remote separations may be necessary in today’s landscape, they fundamentally alter the human dynamics of downsizing Without careful planning, there can be the risk of creating unforeseen risks to the organization
Risks associated with remote separations:
Conducting separations via digital channels can feel less personal and more transactional, presenting the potential risk of miscommunication and the impacted employee developing a sense of disregard or disrespect. Digital channels can feel cold and impersonal, increasing the risk of miscommunication and emotional harm.
Inability to monitor the reaction of employee. While the employer might request the employee be on video for the telepresence call, some employees will opt to keep their camera off. The employer will then not be able to visually gauge the employee’s reaction. Allow the employee the autonomy to participate using audio only if that is their preference. While it is appropriate to request both video and audio, be prepared to proceed with audio alone. In such cases, your attentiveness and listening skills become even more critical, as you will not have access to the employee’s non-verbal cues. You may then choose whether to keep your own video on or turn it off to match the employee’s format.
Confidentiality and compliance risks. Unsecured video connections or misdirected emails may expose sensitive information, while navigating varying local labor laws without face-to-face oversight heightens legal exposure.
Inconsistent support for remote employees. When employees aren’t on-site, organizations may struggle to deliver timely resources—outplacement services, emotional support, technology assistance—which can compound stress and damage morale.
Managerial burden and decision fatigue. Unprepared leaders may adapt or modify the communication style in the moment, learning new platforms and privacy safeguards just as they’re wrestling with the weight of letting valued colleagues go.
Benefits of remote separation:
Protects employee dignity and privacy. Allowing the employee to receive news in their own environment minimizes the risk of public embarrassment (being escorted out of the building) and gives them space to process in private.
Seamless inclusion of stakeholders. You easily can bring in HR representatives, legal counsel and the employee’s manager in one virtual room—ensuring consistency, proper witness to the process, and that all questions are answered addressed in real time.
Preserves nonverbal communication and empathy. Telepresence lets you see facial expressions, body language and tone of voice. These can be critical cues when delivering difficult news. Compared to a phone call or email, it enables a more humane two-way conversation where empathy and clarity can be present.
Increases security and safety at the time of the separation. However, this should not be interpreted that someone may not act out at a later date.
Threat assessment:
For high risk engagements, conduct a thorough behavioral threat assessment to identify any potential risks associated with the individual.
Interview colleagues or supervisors for insights into the employee’s behavior and any previous incidents.
Refer to other steps located here:
Preparing for a telepresence separation:
The key differences between an in-person and telepresence separation are the focus and nature of reviewing the potential risks to your organization because the employee may not regularly, if ever, be physically on-site Many of the planning considerations and coordination items outlined earlier in this guide are applicable to conducting remote involuntary separations Conducting a high-risk separation remotely, particularly in the context of behavioral threat assessment and management, requires careful planning and execution Here’s a list of recommended protocols:
Confirm that the person who will handle the separation discussion is trained and fully prepared with managing the process.
Communication
-
The decision to conduct a remote separation should have already been communicated to upper management and HR, with the goal of assessing whether there is potential for a negative reaction. Remote separations should not be carried out impulsively; they require careful, thoughtful planning. With so many considerations and potential distractions, security should be involved at the onset of the process. Security leaders should proactively engage with HR and offer support throughout the process. They should also communicate any concerns related to “red-flagged” personnel who may pose a risk to the organization.
-
Use your usual channels for communicating the message and conducting the meeting. To keep things streamlined, use the routine system and calendar invitation process.
-
Assemble a threat management team for separation planning, assessment, and management that could/should include, but is not limited to HR, security personnel, associate relations, the threat manager (if this is a separate role), and/or the leadership/supervisor/manager involved—this should make up your core high-risk separation team. Legal should be a consulting member of the team as needed.
-
Refer to document for additional information on the threat management process.
Consult your information technology (IT) staff whenever there is concern with the employee’s access to data systems, especially if the employee works in IT. Ensure that a separated employee’s access to their computer or laptop is shut off immediately prior to the separation. Additionally, deactivate any access passes, cards, fobs, key codes, etc., immediately following separation. However, keep in mind that these steps may need to occur tactically.
Asset assessment
-
Ensure there is a way for them to return work items by issuing a prepaid package return slip to them.
-
Before a remote separation meeting, audit the departing employee’s system access—applications, networks, databases, file shares and cloud services—and temporarily revoke or restrict any active privileges to prevent malicious damage/sabotage. Unlike an in-person termination, where you can physically secure devices, a remote user may have multiple open sessions and files, risking the rapid deletion, alteration or exfiltration of sensitive data. Conducting this review in advance helps prevent data loss, unauthorized changes and other security breaches during the separation. Determine if there is a way for you to compartmentalize network access, so they can use select services and communicate with employees without access to other company resources.
Questions to consider:
-
How will you terminate network and computer access?
-
How fast can it be done?
-
Does it require actions such as locking or restarting a computer?
-
What data is resident on employees’ machines?
-
How will personal contacts be distributed?
-
What about mobile technologies?
-
How will equipment be returned?
-
What is the org willing to part with should the situation escalate and items intentionally retained? Are there red lines (laptops, etc.), or are you willing to part ways with items if the former employee refuses to cooperate? Steps to collect might be considered escalatory/retaliation and could create an opportunity for an additional grievance.
-
Are there risks associated to a refusal to return equipment?
-
Return kit?
-
Courier?
-
-
Pre-paid shipment?
-
Do they have corporate credit cards?
-
Timing/Logistics
-
These considerations, and others, do not lessen the need for respect and sensitivity; rather, they highlight the additional risks of meeting virtually rather than face-to-face. The same vulnerabilities that remote or hybrid employees encounter in their daily work also apply to the termination and separation process.
-
The fundamental logistics: a specific date, time, and communication channel (e.g., Zoom, Teams, or a direct phone call). Treat this just as you would an in-person meeting. Schedule the meeting at a mutually convenient time that still lets the employee reach colleagues. Avoid the end of the work week for the person to be separated and holidays, when staff availability and support resources may be limited.
-
Always confirm and reconfirm the appointment in the employee’s local time zone, and include clear dial-in or join instructions in the calendar invitation.
Remote Separation Protocols
-
- Meeting tools
-
Video meetings are preferred to telephone or audio only meetings.
-
Have a backup to the video conference in the event of failure.
-
Choose a secure and private method for communication to minimize the risks of escalation.
-
Use encrypted channels when sharing sensitive information about the separation.
-
Consult legal on whether or not you can record the meeting.
-
Review one-two party state laws.
-
Video
-
Ask the individual to activate their camera to help ensure they are in a safe location, but present this as a choice rather than a demand. Offering this small measure of autonomy in an otherwise uncontrollable situation can foster trust, reduce the likelihood of early confrontation, and help set a respectful, non-adversarial tone—especially when paired with an explanation that the employer or HR team will be keeping their camera on.
-
-
-
- Recording
-
Ask that you are not recorded or to advise of the recording.
-
There are other potential vulnerabilities to include unknown or nonconsensual recordings, individuals off-camera that are present, or live broadcasting of the meeting. Emphasize during the meeting that policies/procedures, such as our social media policies, apply to this discussion.
-
Assume that your meeting is being recorded, and plan accordingly. They may have others in their space listening and/or they may be recording or live streaming the meeting from another device out of your view. Such recordings regularly show up on social media.
-
-
Reasons to record
Things to consider:
-
Provide recording to person – assuming corporate policy permits it. Contingent on policies and legal counsel. Discuss two party/one party states and countries.
-
Any document that we want to share should be recorded, to show via chat logs, telepresence.
-
Consider survey questions to support the communication process, which can be recorded. Items such as confirmation on receipt of benefits, policies, agreement to return/keep equipment, final pay, etc.
-
-
Discuss AI transcription possibilities.
Telepresence platform choice:
-
Select an appropriate video conferencing platform that allows for clear communication and has security features in place.
-
Consider implementing actions that will limit who can join the meeting or to be notified of who is joining the meeting (e.g., disabling the forward meeting function, using password protection, having the host admit all invitees). Don’t cross your arms (appears defensive), glance away or multitask. Give the person your full, uninterrupted and respectful presence.
Pre-testing:
-
Test equipment, camera, sound, prior to event. Confirm microphone intelligibility, camera, latency, etc.
-
Back-up, phone call, call in numbers in case of technical or network challenges on either side of the conversation.
Neutral Location:
-
If possible, conduct the separation in a quiet environment (a private office).
Timing:
-
While you have planned extensively, initiate the separation with no notice. Scheduling a separation discussion will provide an opportunity for the person to create defensive/offensive plans.
-
Schedule the separation for less disruptive hours and when anticipation of other employees’ reactions is lower. A separation in the middle of the work week offers advantages.
Preparation of Materials:
-
Prepare all necessary documentation (separation letter, final paycheck details, return to site communication, severance package) and ensure that materials are sent securely. Provide a timeline of when to expect these items. Confirm their preferred address; sometimes they do not prefer the address you have on file, or their address may have changed.
Trespassing
-
If the threat management team advises it and no trespassing policy exists, consider issuing a trespass notice. This may not always be advisable, especially if the space they may target is publicly accessible. If it is decided to issue a no return to work notice, issue it upon termination to reduce escalation down the road in lieu of mailing one later without advising the individual.
-
Rehearse:
-
Rehearse. Rehearsing is about managing risk, ensuring compassion, and protecting your organization. Here’s why you want to enter this conversation prepared:
-
Demonstrate empathy and respect.
-
Prepare for if someone acts out and how to respond.
-
Prepare for tough questions.
-
Prepare for unexpected questions or reactions. If concerning direct or indirect comments/veiled threats occur, be prepared to ask for clarification and/or their commitment by setting limits and defining expected behavior during the meeting/discussion.
-
-
Structure the conversation and keep it short and focused.
-
Rehearse tone and body language.
-
Know what resources that you can provide.
-
Clear Communication:
-
Start the meeting by introducing persons present, as well as persons who will join late.
-
Have an agenda, but not one visible to the person being separated. Multi-screen monitors can support this.
-
Request, but do not mandate the employee turn on his camera. It’s okay if they refuse. Ask the person where they are. Be acutely aware of background noises or visuals, which may indicate they intend self-harm.
-
Telepresence Employer Body Language
-
Remove distractions, face the camera, be attentive.
-
Use computer cameras, not conference room cameras, as distance can come across as impersonal.
-
Maintain eye contact.
-
Ensure the application is on monitor that is associated to camera (i.e. face the camera).
-
Adopt an open, forward-leaning posture.
-
Use purposeful, measured gestures.
-
Facial expressions, provide empathetic expressions, let them know you’re listening.
-
-
Use a respectful tone focused on the future, and avoid the perception of being condescending or overly casual. Keep your hands and upper torso in frame so natural gestures reinforce your message. Avoid fidgeting (tapping pens, shuffling papers), which can read as impatience.
-
-
Eliminate negative body language responses.
Facial expressions and eye movements
-
Eye-rolling
-
Furrowed brow or narrowed eyes
-
Sneer or curled lip
Vocalizations and breathing
-
Heavy sighs or audible exhalations (“huffing”)
-
“Tsk” or tongue-clicks
-
Muted grunts or scoffs
Gestures and posture
-
-
Arms crossed tightly across the chest
-
Turning the body or torso away
-
Tapping or drumming fingers impatiently
-
Foot-tapping or leg-jiggling
-
Tension and fidgeting
-
Jaw clenching or teeth grinding
-
Nail-biting or picking at skin
-
Restless shifting in one’s seat
-
Avoidance signals
-
-
-
Looking away or averting gaze
-
Checking phone or watch repeatedly
-
Packing up belongings before the conversation ends
-
Give them your full, uninterrupted presence.
-
Reaffirm to the person you’re listening
Re-review any questions, concerns and timelines for next communication.
-
-
-
-
- Meeting tools
In a remote separation meeting, nonverbal cues become even more critical. Rehearse the process in advance, build a clear script, and circulate an agenda so everyone knows what to expect. Set firm but empathetic boundaries, pausing regularly to allow the employee to absorb this difficult news. Further, keep your focus squarely on the monitor the telepresence application is running on, not on other monitors. Conduct the conversation concisely. Look the person in the eye, speak clearly and directly, and preserve their dignity by maintaining a neutral expression. Don’t rush; allow time for questions, and ensure you don’t smirk in this serious occasion.

APPENDIX C
REMOTE/TELEPRESENCE SEPARATION CHECKLIST
Conducting a separation by telepresence differs from in-person separations The ability to observe the person being separated regarding their reactions, body language, etc , poses a greater challenge than inperson separations A remote/telepresence separation should not be done impulsively and like an in-person separation requires planning
Designed to work in support with the Involuntary Separation Checklist, the following Remote/Telepresence Separation Checklist provides specific questions to consider when a decision has been made to separate an employee remotely or via telepresence
| Questions to Prepare for a Telepresence Separation | Notes |
|---|---|
| Has the decision to separate an employee remotely been communicated to upper management/HR? | |
| Although being conducted remotely, would this separation be considered a high-risk separation if performed in person? | |
| Does the organization have the technology to conduct a remote/telepresence separation? What is the technology platform? | |
| Is the person conducting the telepresence separation trained and prepared to perform this type of separation? | |
| Has security been notified or consulted regarding this separation? | |
| Has the IT department been notified or consulted to ensure they can remotely terminate the employees’ access to networks, data systems, etc. if the employee has access to these systems remotely? | |
| Can the IT or security department deactivate access to an electronic access control card, fob, or key codes if the employee has these items? If yes, how fast can this be done? Will this also deactivate access the employee may have via their mobile device (cell phone, tablet, etc.)? | |
| If the employee has access to a corporate credit card, can the card be deactivated by the Finance (or appropriate) department? | |
| Has it been determined how the organization will recover its physical property (e.g., laptop, computer peripherals, access cards, keys, corporate credit card, etc.)? Return kit? Courier? Pre-paid shipment? What if the organization’s property cannot or will not be returned? | |
| If the employee is working remotely, is IT monitoring the employees’ network access and use prior to the remote/telepresence separation meeting? | |
| Has the IT department conducted an audit of the departing employees’ system access? What data does the employee have access to? | |
| Has the IT department restricted network and system access? | |
| Will the meeting be conducted by telephone or video conference? | |
| Is the method of communication secure to avoid the sharing or leakage of sensitive information? | |
| If being conducted by video conference, has a back-up platform been identified in the event of failure to the primary platform? | |
| Will the meeting be recorded (audio/video)? Has your organization’s legal department been consulted regarding legality concerns? | |
| Has a location been selected to ensure the privacy of the members conducting the separation meeting? | |
| Has the right representative of the organization been selected to conduct the separation meeting? Is this person prepared to conduct this meeting? | |
| Will there be a management witness(s) at the meeting? If yes, have they been identified and briefed accordingly? (Only people necessary to the meeting should be present.) | |
| Have all materials needed for the meeting been prepared and reviewed? | |
| Has the general agenda of the meeting been rehearsed? |
| During the Telepresence Separation Meeting | Notes |
|---|---|
| Be sure to activate the video camera on your computer. Do not use a conference room video camera. | |
| Ask the employee to activate their video camera. | |
| Ask the employee not to record the meeting, however, assume it is being recorded. | |
| Start the meeting by verbally introducing the agenda (the Agenda should not be seen by the person being separated). | |
| Ask the employee where they are (location). | |
| Communicate clearly and directly, but with empathy. | |
| Be aware of your body language and other distractions. (Rehearse prior.) | |
| Be aware of the person being separated and their body language. Document body language. | |
| Conclude the meeting with a summary of key points and explain next steps and note follow-up correspondence and assistance (if any). | |
| Document the meeting. |
APPENDIX D
ESTABLISHING LAW ENFORCEMENT PARTNERSHIPS
Effective collaboration between private sector corporate security and public law enforcement is widely recognized as a cornerstone of public safety The following best practices – organized by day-to-day operations, crisis response, and intelligence sharing – outline actionable steps to build and sustain these partnerships across various sectors These approaches are drawn from government programs, industry standards, and proven strategies across multiple regions This practical guide provides guidance on how to proactively build and sustain positive, professional relationships with local law enforcement agencies (LE) This guide is designed to support your threat management program by strengthening community ties before a critical incident occurs, ensuring faster response, better collaboration, and a more secure environment
Guide for Behavioral Threat Managers: Building Effective Law Enforcement Partnerships
Why This Matters:
Proactive law enforcement partnerships are foundational to a robust threat management program. In times of crisis, such as potential workplace violence, high-risk separations, or domestic violence concerns, any organization will want law enforcement to recognize your site, trust your team, and already have open lines of communication.
When law enforcement already knows your site, personnel, and security expectations, they may respond faster and will respond more effectively during emergencies. Joint drills and pre-event planning ensure tactical units have the information they need when they need it.
Local law enforcement agencies bring deep operational expertise to threat mitigation. Through coordinated engagement, companies can integrate law enforcement knowledge into their internal training, such as armed assailant, tactical awareness, and mental health response. Departments often have community education teams or tactical units willing to run joint sessions, evaluate your plans, or speak to your employees.
Law enforcement can also provide feedback during site-specific risk assessments, especially regarding physical security vulnerabilities, local crime patterns, protest risks, and insider threats. Their participation strengthens your analysis and provides external validation.
Challenges to consider with developing LE relationships:
Private entities may be reluctant to share sensitive data (e.g., surveillance footage, internal reports) due to privacy, liability, or competitive concerns.
Law enforcement hesitancy: Agencies may also restrict sharing due to open investigations or evidentiary rules.
Behavioral teams focus on de-escalation, intervention, and care, while law enforcement emphasizes public safety, enforcement, and containment.
Corporate environments may prioritize business continuity or public image, while law enforcement must follow protocol and statutory mandates.
Over-response and under-response relating to wellness checks, safety checks, and case management.
Lack of communication with threat management team.
Business case for law enforcement relationships
Provides a pre-established point of contact to consult for potential guidance on various issues, not only behavioral management. Adds tactical realism to internal training and exercises.
Enhances the credibility of risk assessments.
Can acts as a deterrent.
Promotes shared goals around employee and community safety.
Can enhance the site’s security culture and can potentially add positive impact and talent retention.
Core Principles
1. Establish Relationships Before You Need Them
Amat Victoria Curam – “Victory loves preparation.” Aim for familiarity and trust before an emergency.
Patrol officers and detectives should know who you are, where your site is, and that your business values public safety and partnership.
Understand resources:
Are off-duty/contracted police services optional through off-duty officers for temporary coverage accessible? Will they provide directed patrol, parked patrol cars, canine detection units for elevated threat conditions (i.e., during involuntary separation)?
How does the local agency collaborate with private sector threat management teams?
2. Lead with Respect and Community Support
- Show your site is a community partner, not just a private entity asking for help.
3. Think Holistically
- Extend engagement to fire departments, EMTs, and mental health crisis responders as part of a complete emergency response framework.
4. Day-to-day Operational Collaboration
- Strong partnerships are forged before the crisis. That starts with relationship-building in everyday operations.
- Introduce yourself and your team to your local police department’s business or community liaison officer. If no such position exists, identify a local patrol supervisor or precinct commander and initiate contact. Offer a briefing on your facilities, risk profile, and concerns—then keep that relationship warm with periodic calls, lunches, or site visits.
- Create mutual benefit. Share helpful resources with law enforcement, such as site access, surveillance footage, or training space. In return, request patrol support or consultation on emerging risks. Reciprocity builds operational trust.
- Provide building layouts, gate access instructions, keyholder contact lists, emergency utility shutoffs, and shelter locations. Even if no formal registry exists, offer that information proactively. Give officers guided tours to increase familiarity.
If your company operates across multiple jurisdictions, build relationships with each local agency. Don’t assume that one point of contact is enough. Agencies tend to prioritize their response according to the nature of the incident type.
Invite officers to company-wide safety briefings, tabletop exercises, or drills. Offer your facility as a venue for tactical team exercises. If officers see the layout before a crisis, they’ll move more confidently and effectively when duty calls.
Follow your local department’s social media for real-time updates. Consider donating meals, hosting informal coffee meetups, or recognizing officers for exceptional service. These gestures create visible goodwill and deepen informal contact.
Partner with nearby businesses to form local public-private task forces or industry alliances. Examples include crime prevention roundtables, downtown safety partnerships, or organized retail theft coalitions. If your industry has a sector-specific law enforcement working group, participate actively.
Day-to-day operational collaboration:
Builds familiarity between officers and your facility.
Establishes key contacts before emergencies happen.
Demonstrates visible appreciation and goodwill.
Encourages patrol presence and deterrence.
Integrates officers into the culture of your site.
5. Working with Law Enforcement to Pursue Criminal Charges or Restraining Orders
In some cases involving employee separation, law enforcement involvement might not involve pursuing criminal charges. In cases where an organization is seeking to pursue criminal charges in a threat assessment case, it is wise to gather relevant information (e.g., detailed case history, communications such as emails, letters, posts, voicemail messages) and present the information on a flash drive or other organized manner to law enforcement, when possible.
Organizations might be able to pursue the case in various jurisdictions, such as where the victim (organization) is located vs. where the employee is located (if different) or federally. Based on the strength of the case, an organization might opt to speak with different law enforcement agencies to understand what criminal charges might be pursued in their jurisdiction based on their laws. If a criminal case is pursued in the jurisdiction where the organization is located, and this jurisdiction is different than where the employee is located, the employee might travel to that jurisdiction for the criminal case (which might result in encounter attempts, etc.). Therefore, it is important that any victims are aware of this possibility.
When law enforcement is given a criminal case to investigate, the case is then managed by law enforcement. Law enforcement’s goal is public safety, while an organization’s goal might be the safety of its employees, vendors, and customers. The organization may request that law enforcement take, or not take, certain actions, though it is wise to recognize that law enforcement will pursue actions they feel are best for public safety.
Also, if an employee is detained due to an arrest or mental health hold, recognize that the employee could be released quickly, even within hours, based on the circumstances of the case. In some situations, law enforcement might agree to notify you prior to the employee’s release from custody. The goal of this document is not to explore all case management strategies and the pros and cons of each. Certain intervention strategies might escalate a case. That said, based on the laws, witht hreat management, legal team approvals, etc , it might be possible to pursue a criminal stay away/ protective order for the victim via the criminal case and/or pursue a civil restraining order Note: only some states allow businesses to apply for orders of protection on behalf of their employees and the employee should always be supportive prior to applying.
- The organization should realize that the petitioners’ target’s address and other information will more likely than not be made available to the person being separated It is strongly suggested that an organization’s legal department is part of this decision process
Step-by-Step Action Plan for LE Relationships
1. Obtain organizational buy-in
Communicate intent to create LE relationships and gain approval.
Establish policy/procedures that require these relationships at a site level and communicate the intent to employees.
2. Identify the owner of the relationship
Identify the person or persons at your site or sites that is responsible for creating and maintaining LE relationships and contacts for when they may be needed. It should be noted that the LE point of contact may change and that your company representative should ensure that information is up-to-date by periodic communication with the respective agency(s).
3. Who responds to emergencies
Identify your LE reporting jurisdictions. In some instances, locations can have more than one responding LE agency.
4. Join, participate, and attend intelligence sharing and specialized partnerships
Every region has a fusion center. These facilities collect and analyze suspicious activity reports, cyber intel, and threat patterns. Private sector entities can request access to unclassified briefings and participate in joint exercises.
Join FBI InfraGard to access bulletins, webinars, and sector-specific alerts. Participate in Information Sharing and Analysis Centers (ISACs) to connect with other companies in your vertical.
Participate in Domestic Security Alliance Council (DSAC). DSAC is a federal public-private partnership between the FBI, DHS, and U.S.-based companies with significant economic or national security impact. It offers a secure channel for classified and unclassified threat intelligence and facilitates direct collaboration between corporate security executives and federal law enforcement.
Engage with organizations like ASIS International or Association of Threat Assessment Professionals (ATAP). Local chapters often include law enforcement liaison committees that offer structured, recurring opportunities for contact between private security professionals and police officials.
5. Mentor private sector career paths for public LE retirees
Offer mentorship and transition assistance to officers moving into the private sector. Engage in police advisory boards or public-private crisis working groups when available. Provide your facility for use during drills or community training programs.
6. Initiate executive-level contact with responding LE organizations
Have your site leader send a formal introduction letter to specialized units (behavioral health, crimes against, etc.) persons or LE leadership (i.e., Police Chief or Sheriff).
Ask the Chief or Sheriff to introduce you to the local precinct commander or patrol supervisor for your area. From there, request a primary point of contact to streamline future communication.
Log their contact info, preferred communication method, and schedule periodic touchpoints (turnover and movement is frequent in law enforcement).
Other ideas include:
Create LE appreciation events, such as open house, tours or support LE volunteer efforts.
Extend employee discounts to local officers, where appropriate.
If your company has a philanthropic arm, offer to fund small-scale LE initiatives (e.g., CIT training, trauma kits).
Invite LE to workplace events
When hosting employee meals or events, invite patrol officers to join. It shows inclusiveness and goodwill. Even if LE do not attend, the gesture matters and builds positive sentiment.
Offer your site for use
As allowable, offer your facility for tactical training (i.e. with proper planning, allow police tactical teams to train on-site during off-hours).
Designate reserved LE parking near your building entrance, visible and symbolic.
Allow officers to use your café, breakroom, fitness room or parking lot for brief stops.
Send/recognize police efforts
If an officer responds to your site, get their name and supervisor’s contact info.
Send a quick note of appreciation (not just “badge number requests”).
Seek to identify mutual objectives.
Seek to learn how LE will respond to an active threat. What is the process? Does it match your organization’s intent?
Do not bring criticism, this is relationship-building, not complaint resolution.
7. Crisis response coordination
When an emergency strikes, pre-established relationships are the difference between chaos and coordinated action. Joint planning, training, and defined roles pay off.
Work with law enforcement to develop emergency response plans for active shooters, bomb threats, natural disasters, or protests. Clarify respective roles and capabilities before a crisis unfolds.
Conduct regular joint drills—tabletop exercises, evacuation simulations, or full-scale active shooter scenarios. Invite police to lead parts of the training or provide after-action feedback.
Exchange 24/7 emergency contact numbers with local police leadership and designate internal company contacts for specific response roles. Confirm this information regularly and embed it in your internal crisis playbooks.
Before any incident, make sure first responders have what they need: floor plans, door codes, camera locations, shelter-in-place spots, alarm panel instructions, and utility shutoffs. Consider creating a physical or digital “emergency pre-plan” packet.
Crisis response coordination:
Reduces confusion during fast-moving incidents.
Builds operational interoperability with first responders.
Enhances officer confidence during site response.
Provides clearly defined responsibilities and command roles.
Ensures faster, better-informed tactical decisions.
| Action | Frequency | Owner |
|---|---|---|
| Send an intro letter to Chief/Sheriff | 1x per year or site change | Site Leader |
| Host meet-and-greet with local precinct | 1x per year | Threat Manager |
| Maintain LE contact info and check in | Quarterly | Threat Manager |
| Invite LE to company events | Ongoing | Site Coordinator |
| Organize appreciation meals | 2x per year | Human Resources/Security |
| Participate in neighborhood partnerships | Ongoing | Site/Corporate Security |
Summary:
Trust does not come from one meeting, one email, or one drill It comes from repeated, meaningful contact, day after day, month after month Private sector security leaders who invest in authentic, functional relationships with law enforcement build more resilient organizations and safer communities These partnerships are not optional anymore They are operational necessities
SURVEy
Get Involved!
Welcome to our comment section. Please share your experiences, how our guide assisted you, or any insights for the community. Your contributions enhance our collective expertise and professional development.
With exception to Ahrens Security, any organizational or business affiliation or endorsement is not intended and should not be inferred. Document is free to all, but is not to be used for commercial purposes and may not be sold. © Copyright 2025 – All Rights Reserved | Privacy Policy | Terms of use

